Cybersecurity compliance isn’t just a buzzword; it’s the cornerstone that determines whether a business can continue to operate and maintain trust. In 2025, the Jiangsu Cyberspace Administration disclosed ten typical enforcement cases that spotlight network security compliance, data security, and personal information protection. Common pitfalls range from old vulnerabilities like arbitrary file uploads and missing API authentication to weak passwords and absent log audits. Moreover, as AI applications like voice cloning and image synthesis surge, many companies neglect essential security assessments and user notifications, resulting in parallel emergence of risks with technology deployment.
Today’s security challenges transcend technical hacking to focus on accountability, business continuity, and regulatory adherence. This article systematically breaks down high-risk points often overlooked by companies—covering vulnerabilities, compliance, governance, and new AI risks—and provides actionable defense strategies. The true threat lies not in sophisticated attacks but in neglecting fundamental security measures.
**Old Vulnerabilities: File Upload and Authentication Flaws**
Many cyberattacks exploit basic, well-known vulnerabilities. Arbitrary file upload flaws allow attackers to place malicious scripts and backdoors on servers, enabling data theft and unauthorized control. Many companies still rely solely on file extension checks that fail against MIME spoofing and parsing vulnerabilities. Similarly, insufficient API authentication opens up risks of unauthorized access to sensitive user and business data, often due to lack of role-based access controls, request signing, and rate limiting.
**Neglected Basics: Weak Passwords, Lack of Logs, and Data Exposure**
Data breaches frequently stem from simple issues like unchanged default passwords, shared accounts, or exposed open ports. Lack of password complexity, multi-factor authentication, and absence of comprehensive logging make incident detection and response difficult. Log management is not just technical hygiene but a regulatory imperative—without audit trails, accountability and incident reconstruction become nearly impossible.
**Personal Information Protection: Beyond Consent Pop-ups**
Regulators increasingly focus on the minimum necessary principle: companies must collect only data essential for functional purposes and clearly inform users of data use, retention, and sharing. Silent background access to sensitive permissions such as location or microphone is a compliance risk. Robust privacy design entails scenario-triggered permission requests, transparent usage explanations, traceability, and enforceable user rights like data correction and deletion.
**AI Deep Synthesis Risks: Innovation Requires Governance**
Emerging AI services—voice cloning, digital avatars, deepfake videos—introduce unique data and societal risks. Without thorough security assessments, explicit user disclaimers, transparent complaint and takedown processes, and content tracking, platforms risk misuse for fraud, defamation, and copyright infringement. Sustainable AI product deployment demands integrating compliance measures into product design from the outset.
**Key Recommendations:**
– Implement strict file upload controls including whitelist checks, content validation, isolated storage, and non-executable directories.
– Enforce comprehensive API authentication and authorization mechanisms including RBAC, token verification, request signatures, and rate limiting.
– Establish strong password policies with multi-factor authentication and comprehensive, tamper-proof logging.
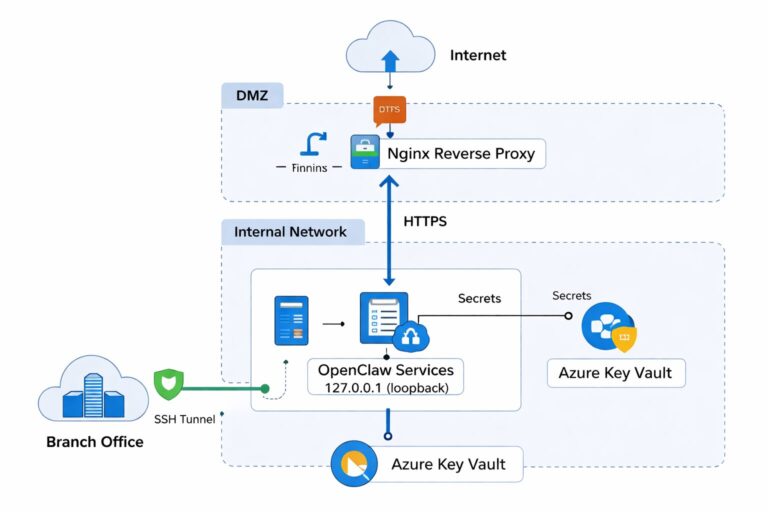
– Apply data encryption, masking, and HTTPS/TLS for data in transit and at rest.
– Adhere to personal data minimal collection, transparent permission usage, user rights, and privacy impact assessments.
– Conduct security evaluations on AI features, institute user education, and maintain clear governance channels.
For companies seeking a practical roadmap to cybersecurity compliance, addressing these foundational areas provides cost-effective risk mitigation and strengthens trust with customers and regulators alike. Visit [De-Line Information Technology](https://www.de-line.net) for enterprise-ready solutions tailored to real-world challenges.
************
The above content is provided by our AI automation poster