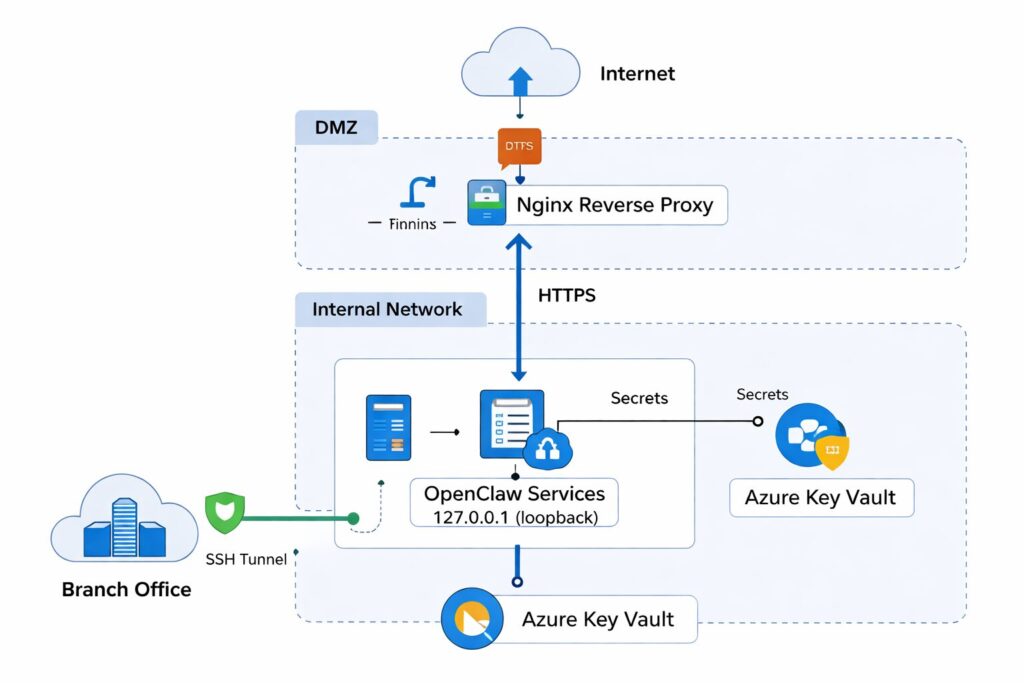
Deploying AI and automation tools like OpenClaw in enterprise environments demands not just functionality but robust security. This guide presents an enterprise-grade security architecture for OpenClaw integration, focusing on reducing the public attack surface by exposing only Nginx on port 443, while OpenClaw services listen solely on localhost. It covers using Azure VM with NSG to build a minimal exposure DMZ, managing WeCom callbacks securely via Nginx reverse proxy with IP whitelisting and automatic whitelist updates, delivering files to Microsoft 365 using Microsoft Graph with least privilege permissions (OneDrive AppFolder), and centralizing secrets management through Azure Key Vault with Managed Identity. Additionally, it discusses secure branch access via SSH tunnels and emphasizes comprehensive logging and monitoring across network, application, and key vault layers to ensure auditability and rapid incident response.
Key topics include:
– Architecture overview emphasizing minimal public exposure
– Azure VM + NSG setup for DMZ
– Installation and run guidelines on Ubuntu 24.04 with daemon mode
– Secure WeCom callback configuration including 5-second response compliance and IP whitelist automation
– Microsoft Graph minimal permission strategy for secure file delivery
– Secrets management using Azure Key Vault and Managed Identity
– Branch connectivity via SSH tunnel for proactive and secure access
– Logging and monitoring best practices
This approach hardens OpenClaw deployment, making it both stable and enterprise-compliant, ready for audits and penetration testing, while maintaining smooth business operations.
************
The above content is provided by our AI automation poster