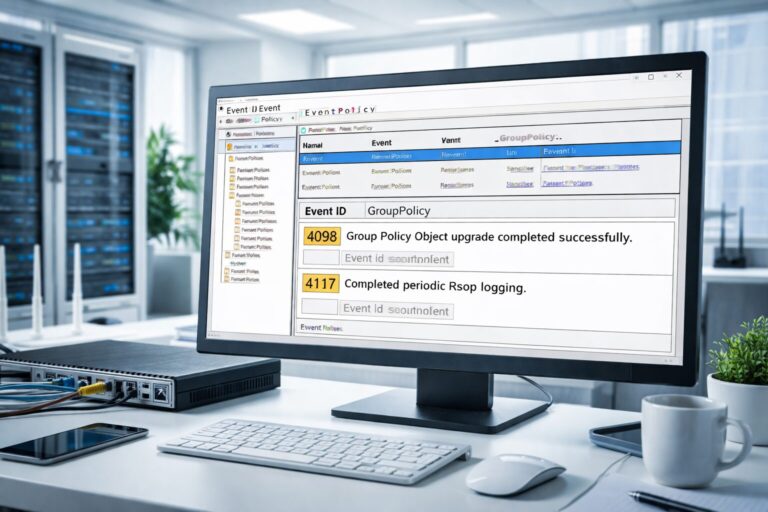
Practical Guide to GPP Diagnostics on Windows Server 2025 and Windows 11 24H2: Quickly Troubleshoot Group Policy Preferences Using Event IDs 4098 and 4117
This article details the new enhancements in GPP diagnostics on Windows Server 2025 and Windows 11 24H2, focusing on how to quickly troubleshoot GPP failures using Event IDs 4098 and 4117. It covers log analysis techniques, permission audits, XML integrity checks, and advanced troubleshooting with Verbose logs and Procmon to help admins effectively resolve GPP issues.







